Email Authentication Basics
After writing a blog post on Brand Indicators for Message Identification (BIMI), I realized that simplifying the other three email authentication protocols could be helpful.
SPF (Sender Policy Framework)
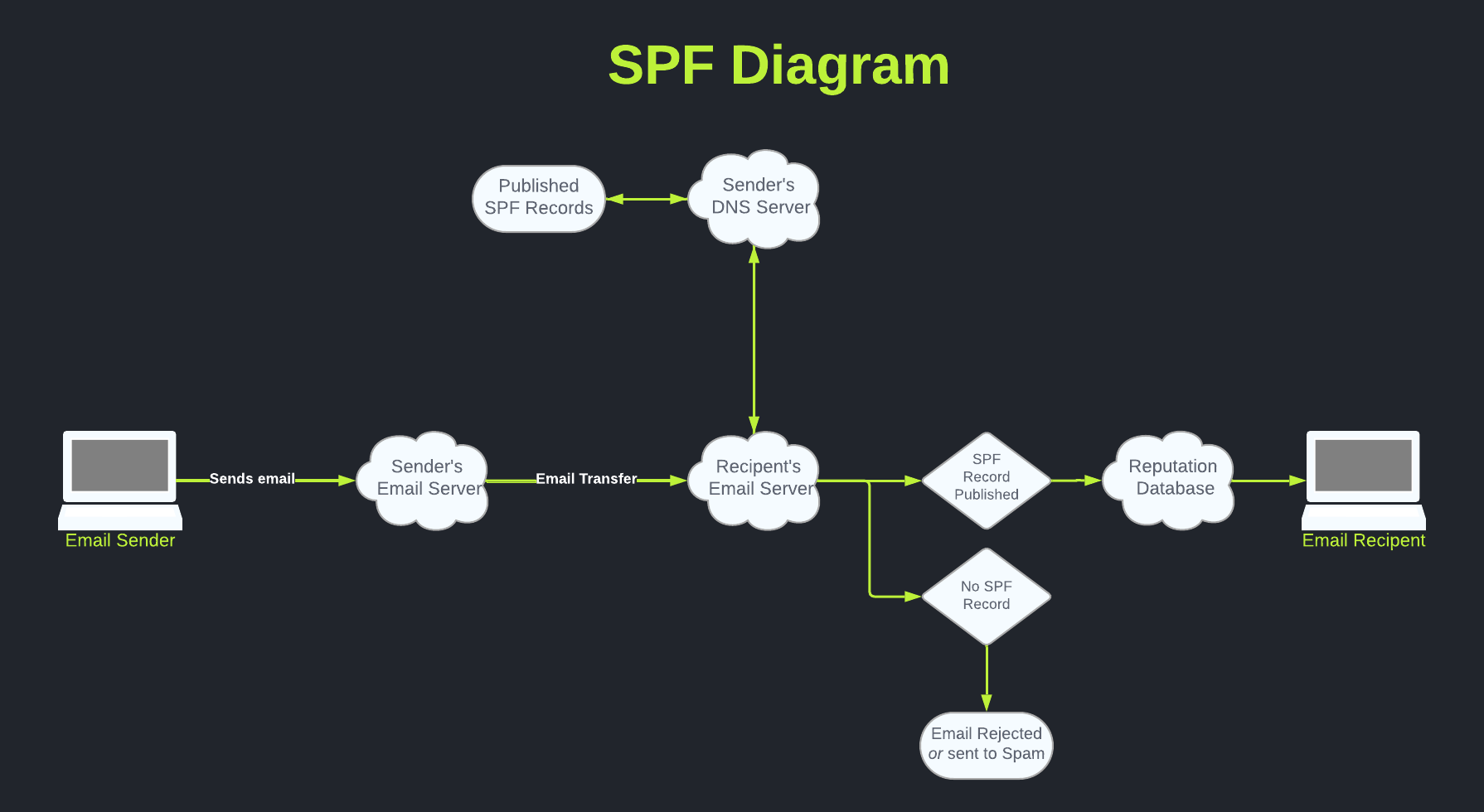
SPF acts like a bouncer at a fancy club; if you're not on the list, you can't enter.
SPF is a list of approved senders for a domain. When an email arrives, the receiving server checks if the sender's server is on its approved list. If it is, the email passes the SPF check.
Example SPF Record
You can add SPF records to your DNS server as TXT records. For example:
v=spf1 include:_spf.google.com ~all
v=spf1: Specifies the version of SPF.
include: This tag indicates that this particular third party is authorized to send emails on behalf of your domain.
Simple enough, but what if you want to include IP addresses instead of domain names? In this scenario, you would use the ipv4: tag.
v=spf1 ip4:192.168.0.0/16 include:_spf.google.com ~all
DKIM (DomainKeys Identified Mail)
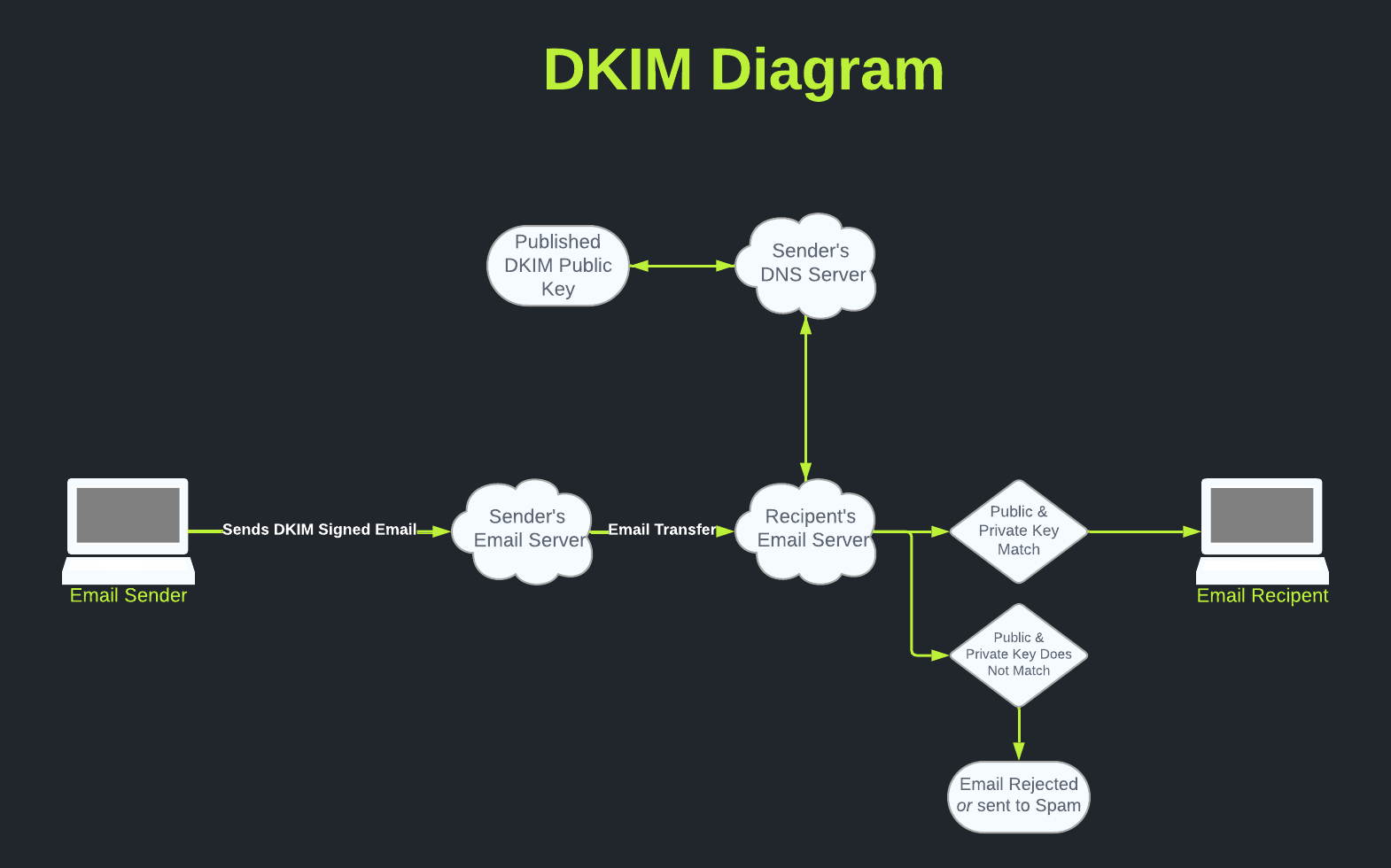
SPF records are designed to prevent spoofed emails from being sent to recipients. However, SPF offers no assurance that a message has not been tampered with in transit.
DKIM uses a digital signature to ensure email integrity. The sender's private key signs the message, and the recipient verifies the signature with the sender's public key, ensuring the message hasn't been altered.
Example DKIM Record
The DKIM TXT record, which includes the Name and Value, is provided by your email service provider. It will look similar to the example shown below:
Name:something._domainkey
Value: v=DKIM1; k=rsa; p=MITBIjAXCgaqhkiG9w1BAQEFAAOCAQ8AMIIBCgKCAQEBmHIL2Q4RdLKmXGzjFosz5ec0ZVgyHriELHzkyGYoOH+9QfEQev3tH+Kt82tdy+Q9EaeSiRsShBwTYxGbNtqwPVeHSTOL6UDCloniOsXkCxAP4zqaRanA7TwKaSvKMK2AAajGHmCKgEWnw34f+grlZNyhahS89JXRgXJGd4/bTa/FCXY4kTNAZI41XTMH1EttM
something._domainkey: This is a specialized value issued by the email service provider. It is included in the DKIM header to enable an email server to perform the required DKIM lookup in the DNS.
v=DKIM1: Specifies the version of DKIM.
k=rsa: Indicates the key type, which is RSA.
p=: Specifies the public key for the DKIM record.
DMARC (Domain-based Message Authentication, Reporting, and Conformance)
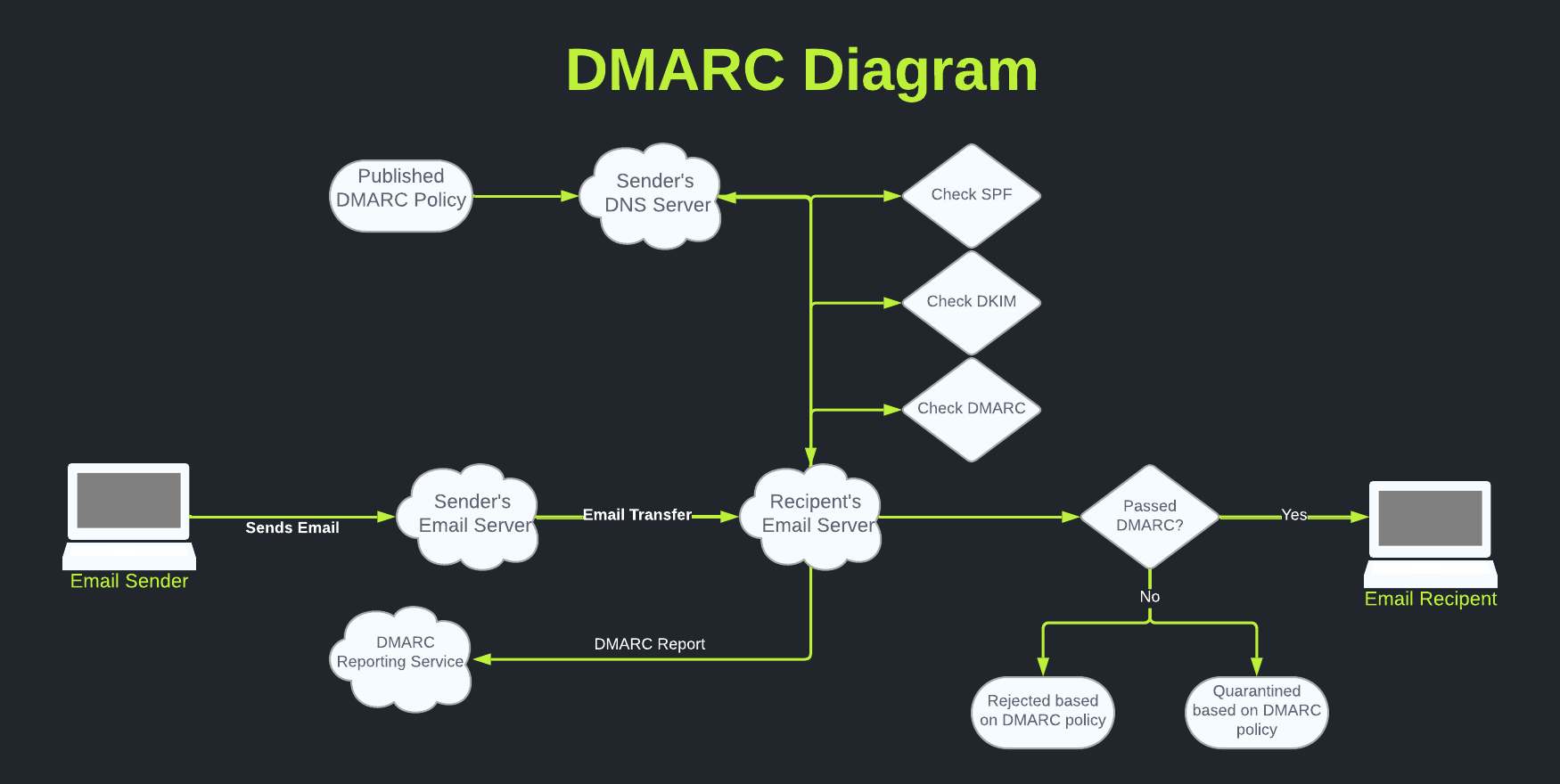
DMARC acts as a supervisor for both SPF and DKIM. It sets rules for handling emails that fail SPF or DKIM checks and reports on email authentication results so you can fine-tune your configuration.
Example DMARC Record
A DMARC record is a TXT record that informs the email recipient of the policy after checking the SPF and DKIM status. An email is considered authenticated if either SPF, DKIM, or both pass. If none pass, the following policies can be configured to manage delivery:
DMARC Policies
None - This policy will only monitor DMARC compliance. No action is taken on messages that fail SPF and DKIM checks.
Quarantine - This policy will send messages to the Spam folder if failing SPF and DKIM checks.
Reject - This policy will reject messages entirely if failing SPF and DKIM checks.
When rolling out DMARC, it's recommended to start with the first policy to identify unknown senders that may require SPF and DKIM configuration. Once you feel confident, enable the Quarantine policy, followed by the Reject policy. This may take some time, depending on how many services send emails on your behalf. The DMARC reports will indicate when you’re ready to upgrade your policy.
DMARC Reports
A DMARC record also instructs email servers to send reports back to the reporting email address listed in the DMARC record. These reports offer valuable insights into all the sources that are sending emails from your domain. This can be extremely helpful when first rolling out DMARC for your organization.
Additionally, I suggest purchasing a DMARC monitoring service to simplify the XML reports you receive. I've personally been using DMARC Digests for the past two years with success. However, there are other options available.
Now that we understand the components of a DMARC record let’s see an example:
v=DMARC1; p=reject; rua=mailto:email@dmarc-service.com;
v=DMARC1: Specifies that the record in DNS is a DMARC record using version 1.
p=reject: The required p tag indicates your DMARC policy.
rua=mailto: This is the designated address where DMARC reports will be sent.
BUT WAIT THERE’S MORE!
If the email passes DMARC and you have BIMI configured, it adds a brand logo to your email to reinforce authenticity.
Conclusion
To summarize, here's a simplified example of how SPF, DKIM, DMARC, and BIMI work together:
So, imagine sending an email from your company:
SPF: You're on the approved sender list.
DKIM: Your email has a unique digital stamp that matches your domain's key.
DMARC: Your supervisor DMARC is okay with the SPF and DKIM results and lets the email through.
BIMI: If you've got all the previous steps right, you might get a cool logo badge next to your email in some inboxes.
A common misconception is that implementing DMARC protects the organization from phishing and spoofing attempts. However, in reality, it protects the email recipients. Therefore, the more organizations that adopt DMARC, the safer everyone will be from malicious activity.